Cybersecurity experts are warning crypto users of a sophisticated malware campaign that has potentially targeted more than 10 million users worldwide through online advertisements promoting fake cryptocurrency trading apps.
Cybersecurity firm Check Point issued a report on their website detailing an ongoing operation they’ve dubbed “JSCEAL”.
The team says the campaign exploits the growing popularity of digital assets by impersonating nearly 50 well-known crypto platforms, including Binance, MetaMask, and Kraken, to distribute malware designed to steal sensitive user data and digital assets, has been around since at least March last year.
How does the Malware Campaign take place?
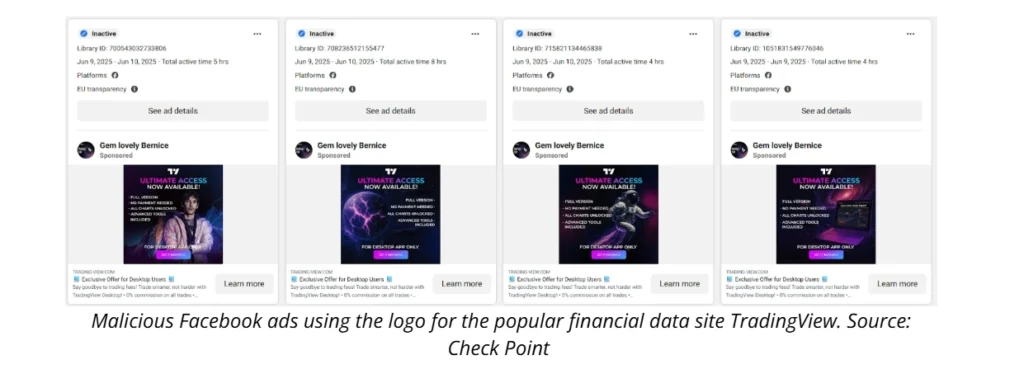
According to Check Point, the campaign used paid advertisements across major social media platforms, particularly using Meta’s ad tools. These ads lead unsuspecting users to counterfeit websites that closely mimic the appearance of legitimate trading platforms. Once a victim downloads the fake application, the malware silently installs and begins harvesting information in the background. More than 35,000 malicious ads were circulated in the first half of 2025 alone.
The firm estimates that at least 3.5 million users in the European Union were exposed to these ads, with the total global reach likely surpassing 10 million due to impersonations of financial institutions across Asia, a region with high social media usage.
“The advertising reach is massive, but it’s important to note that exposure doesn’t necessarily mean infection,” a Check Point spokesperson cautioned.
“Still, the potential for harm is significant.”
How does JSCEAL Malware Campaign Evade Malware Detection?
The JSCEAL campaign employs advanced evasion tactics to avoid detection, including anti-analysis features and unique obfuscation techniques.
The malware is written in JavaScript, allowing it to run without requiring any user interaction. Check Point noted that the simultaneous execution of both the fake installer and a legitimate website further complicates detection by creating a convincing illusion of authenticity.
Once installed, the malware collects a wide array of user data, including:
- Keystrokes that can reveal passwords
- Telegram account credentials
- Browser cookies that track user behavior
- Autocomplete passwords stored in browsers
- Access and manipulation of crypto wallet browser extensions, such as MetaMask
Check Point described their investigation as “challenging and time-consuming”
“This isn’t just another phishing scam; it’s a technically advanced, global operation that’s proven hard to detect and analyze.”
Growing Cyber Security Threats to Crypto Users
The decentralized and anonymous nature of cryptocurrency continues to make it a prime target for cybercriminals. A whopping $3.1 billion in cryptocurrency has been lost in the first six months of 2025 due to security issues like smart contract bugs, weak access controls, rug pulls, scams and malware campaigns.
Meanwhile as technology evolves, the types of cyber exploits also become more complex.
According to an investigation by crypto detective ZachXBT, crypto companies worldwide, may have unknowingly hired over 900 North Korean hackers into the cryptocurrency ecosystem.
The situation is worsened by the fact that once stolen, crypto funds are extremely difficult to trace or recover and that due to the decentralized nature, victims are left with little to no avenues for recourse.
Given the circumstances, Check Point advises users to remain cautious and verify any crypto related apps or websites through official sources to safeguard themselves from malware campaigns of this nature.
“Crypto users must remain vigilant,” the firm concluded.
“These kinds of attacks exploit trust and timing and they’re only getting more sophisticated.”